How to ensure secure wireless communication in remote control systems?
When purchasing wireless remote control systems for industrial, commercial, or consumer applications, security decisions made at design and procurement directly affect safety, liability, and long-term support. This guide answers six specific long-tail questions beginners frequently ask but rarely find authoritative answers to. The explanations reference industry best practices (AES encryption, BLE Secure Connections, Zigbee 3.0, LoRaWAN, signed OTA, secure elements) and provide practical steps to validate vendor claims and harden deployments.
1. How can I verify a wireless remote really uses per-device AES keys instead of an insecure shared default key?
Pain point: Many buyers discover in the field that vendor devices ship with shared or factory default keys, making mass compromise trivial.
Verification steps you can perform or require from vendors:
- Request documentation of key provisioning: Ask for a description of the manufacturing/commissioning process: Does each device receive a unique symmetric key or a unique certificate? Vendors should show a unique device ID tied to a unique key/certificate.
- Ask for a secure element or key injection report: Prefer devices that use a hardware secure element (e.g., Microchip ATECC family) or a dedicated TPM/HSM-backed injection process. Request a certificate or attestation showing keys were injected in a secure environment.
- Require crypto parameters: Ensure the device uses AES-128 or AES-256 in authenticated modes (AES-CCM or AES-GCM) for payload confidentiality/integrity. If public-key auth is used, demand ECDH/ECDSA (P-256) or equivalent modern curves.
- Challenge the vendor with an audit test: Ask for a protocol trace from a packet sniffer (e.g., via an RF protocol analyzer or BLE sniffer) showing per-device nonces and unique session keys. If they refuse, insist on third-party lab verification (EMC/crypto test lab).
- Check for absence of default keys: During acceptance testing, factory-reset two units to ensure they do not revert to the same shared key or fixed pairing code. Shared defaults are a red flag.
Red flags to reject a product:
- Vendor cannot demonstrate unique key provisioning or secure element use.
- Use of unauthenticated encryption (e.g., raw AES in ECB) or plain CRC-only integrity checks.
- Documentation referencing legacy algorithms known to have practical attacks (for example, proprietary “rolling code” systems without public analysis).
2. What practical measures stop replay and relay attacks on long-range sub-GHz remote controls (433/868/915 MHz)?
Pain point: Sub-GHz remotes are widely used because of range, but many legacy implementations are vulnerable to simple replay/relay attacks and signal amplification attacks.
Defenses you should require or implement:
- Strong rolling-code / challenge-response: Use a cryptographically secure challenge-response protocol rather than a simple rolling counter. The remote signs a server-provided challenge or uses a device-unique key to compute an authenticated response (AES-CCM with a nonce). Rolling codes implemented without crypto (or with weak key management) are insufficient.
- Nonces and session freshness: Always include a nonce/timestamp and message authentication code (MAC). Device and receiver must reject stale or duplicate nonces. Time-based approaches require secure clock sync or windowing rules; sequence numbers must be maintained securely and allow resynchronization procedures.
- Relay detection: Implement secondary anti-relay measures if physical proximity matters: use time-of-flight/distance-bounding if hardware supports it, or require a short-range pairing token (NFC/low-frequency) for high-privilege operations.
- RSSI / fingerprinting heuristics: Compare expected RSSI patterns and radio fingerprints; if suddenly signal comes from an impossible RSSI or multipath signature, treat with caution. This is heuristic and should not replace robust cryptography.
- Jamming/anti-jam and FHSS: Frequency-hopping spread spectrum (FHSS) or adaptive channel selection reduces simple jamming and makes relaying harder. FHSS plus authenticated frames is strong.
Testing recommendations:
- Perform a replay test using a basic RF recorder to capture and replay messages; device must reject replayed frames.
- Attempt a relay using two radios spaced apart; acceptance indicates vulnerability to relay attacks.
- Verify resynchronization flow: remote and receiver must support secure resync without exposing a window for replay.
3. How do I ensure OTA firmware updates for remote controls are secure and won't brick my fleet?
Pain point: OTA updates are necessary for security fixes but risky if unsigned images, interrupted updates, or poor rollback policies exist.
Essential capabilities to require:
- Cryptographic signing of images: All firmware images must be digitally signed (ECDSA P-256 or RSA-2048/3072) and verified in-device before installation. Do not accept devices that trust unsigned images.
- Secure boot and verification: Devices should implement secure boot that verifies the firmware signature chain from bootloader to application. This prevents installing tampered images.
- A/B partitions and atomic updates: Use dual-bank (A/B) firmware partitions so the device can roll back to the previous known-good image if update is interrupted. Avoid single-bank designs that can brick on power loss.
- Delta updates and integrity checks: Prefer authenticated delta updates (reduces airtime and battery) but ensure each delta is signed and verified. Validate complete image checksum before switching partitions.
- Rollback protection: Maintain monotonic version counters signed by the vendor/PKI to prevent replay of old vulnerable firmware.
- Robust power-failure handling: Devices should have a reliable bootloader that can enter recovery mode and accept a signed image over a wired or OTA channel.
Operational recommendations:
- Test the vendor's update procedure at scale in a staging environment using representative radios, interference profiles, and battery states.
- Require vendor failure-rate SLAs for updates and a documented rollback plan and update verification logs (device-side and server-side logs).
4. Which wireless technology (Bluetooth LE, Zigbee, LoRa, sub-GHz) offers the best trade-off between security, latency, and battery life for industrial remote controls?
Pain point: Buyers want a single recommendation, but real choices are trade-offs: latency, range, battery life, and built-in security differ across stacks.
Short technology comparison (practical numbers and characteristics):
- Bluetooth Low Energy (BLE, especially BLE 5.x):
- Latency: typically 10–100 ms for connected LE operations; advertising-based commands can be faster but less reliable.
- Range: up to 100 m (line-of-sight) with BLE 5 long-range modes; practical indoor range often lower.
- Power: optimized for low duty cycles; good battery life when used for intermittent button presses.
- Security: BLE Secure Connections (LESC) uses ECDH (P-256) for key exchange; supports AES-CCM link encryption. Good built-in security when implemented correctly.
- Zigbee / Thread:
- Latency: typical end-to-end tens of milliseconds; mesh can add hops and delay depending on topology.
- Range: short per-hop (~10–50 m indoor) but mesh extends coverage.
- Power: good for battery devices using sleep cycles; mesh routing increases complexity.
- Security: Zigbee 3.0 uses AES-128 (CCM) and network/application keys; requires solid key management to avoid shared-network-key issues.
- LoRa / LoRaWAN:
- Latency: milliseconds to several seconds depending on class and downlink constraints; not ideal for low-latency control.
- Range: kilometers in open areas (excellent long-range).
- Power: excellent for infrequent transmissions; longer sleep times.
- Security: LoRaWAN has AES-128 session keys (AppSKey/NwkSKey) but cadence and backend architecture matter; not ideal for millisecond control tasks.
- Proprietary sub-GHz RF:
- Latency: can be very low (<10 ms) depending on protocol and modulation.
- Range: good—sub-GHz penetrates obstacles and offers long range.
- Power: generally efficient for short bursts.
- Security: depends entirely on implementation. Many legacy systems lack authenticated encryption—require AES-CCM with unique keys.
Buyer guidance:
- For low-latency industrial control where security and latency are paramount, BLE or a well-designed sub-GHz proprietary protocol with AES-CCM and unique keys can be best.
- If range with modest latency is needed (e.g., remote asset tracking), LoRa/LoRaWAN works but is not a real-time control channel.
- Choose open standards (BLE, Zigbee, Thread) when interoperability and long-term support matter; require modern security modes (LESC, Zigbee 3.0).
5. What are realistic latency and interference expectations for remote controls in noisy factory environments, and how should I test them before purchase?
Pain point: Vendors quote ideal latencies and ranges, but factory floors introduce metal, reflections, EMI, and co-channel traffic that increase latency and packet loss.
Realistic expectations:
- Latency: In quiet environments, BLE and Zigbee controls can achieve sub-50 ms response times. In noisy industrial settings expect median latencies of 50–200 ms depending on retries and topology.
- Packet loss: You should plan for occasional packet loss up to a few percent in harsh RF environments. Systems must tolerate retries and idempotent commands.
- Range degradation: Metal racks and moving machinery can reduce effective range by 30–80% in problematic spots.
Pre-purchase testing checklist:
- On-site acceptance testing: Run real-world tests in the busiest production areas, during peak shift, with all suspected interferers active.
- Measure distribution of latencies: Use a test harness that logs command send and acknowledgement timestamps to compute 95th/99th percentile latencies, not just averages.
- Spectrum analysis: Bring or ask the vendor for a spectrum analyzer scan to identify busy channels and cross-technology interference (Wi‑Fi, industrial wireless systems). This informs channel selection or FHSS needs.
- Interference mitigation trials: Test vendor features like adaptive frequency hopping, channel blacklisting, and antenna orientation adjustments.
- Battery under stress: Test battery life under real traffic patterns and interference-induced retransmissions.
6. How should I manage keys and certificates at scale (hundreds to thousands of remotes) to maintain a secure lifecycle?
Pain point: Small deployments can be managed manually; larger fleets require automated, auditable key lifecycle management to avoid expired certs, orphaned devices, or key leakage.
Recommended architecture and practices:
- Device identity and manufacturing: Inject unique device credentials during manufacturing using a secure key injection facility or secure element per device (ATECC608A or equivalent). Maintain an immutable record of device IDs and public keys in a provisioning database.
- Use a PKI and HSM: Host root and intermediate keys in a Hardware Security Module (HSM). Issue device certificates with limited lifetimes and use an automated PKI for enrollment, renewal, and revocation.
- Automated provisioning: Implement secure zero-touch provisioning using protocols like EST/SCEP or manufacturer-supplied secure commissioning. Ensure private keys never leave secure storage on devices.
- Key rotation and revocation: Plan for periodic key rotation and implement revocation mechanisms (CRLs, OCSP-style checks, or short-lived certificates) and a secure OTA workflow for distributing new trust anchors if necessary.
- Device management platform: Use an MDM/IoT security platform that tracks device state, certificate expiry, firmware versions, and supports remote revoke/wipe commands.
- Auditing and logging: Keep immutable logs (SIEM) of provisioning, key issuance, and OTA operations. Regularly audit access to PKI/HSM and maintain separation of duties.
Operational considerations:
- Define SLAs for certificate expiry notifications and automatic renewal processes to avoid downtime.
- Test key compromise scenarios and rehearse device revocation and mass-reprovisioning flows in a sandbox before live rollouts.
Concluding summary: Advantages of secure wireless remote control systems
Investing in secure wireless remote control systems that implement per-device keys, authenticated encryption (AES-CCM/GCM), signed OTA with secure boot, and hardware-backed key storage reduces the risk of unauthorized control, replay/relay attacks, and large-scale compromise. The right wireless technology balances latency, range and battery life: BLE or modern sub-GHz designs for low-latency control, Zigbee/Thread for mesh-interoperability, and LoRa for long-range low-duty telemetry. Operational benefits of a secure approach include predictable device behavior in noisy environments, manageable lifecycle operations at scale through PKI/HSM and MDM, and reduced legal/operational exposure from security incidents.
Procurement checklist recap (use when evaluating vendors):
- Proof of per-device unique keys and secure provisioning
- AES-CCM/GCM authenticated encryption and modern key exchange (ECDH/ECDSA)
- Signed OTA + secure boot + A/B update partitions
- Support for FHSS or adaptive channel selection for interference mitigation
- Hardware secure element support and documented lifecycle (rotation/revoke)
- On-site acceptance tests for latency, packet loss, and firmware update reliability
If you need a validated secure wireless remote control system or a custom RF solution with AES encryption, rolling-code hardening, BLE/Zigbee/LoRa options, signed OTA and PKI-backed lifecycle management, contact us for a quote. Visit www.systoremote.com or email [email protected].
CRC2605V
Can I customize the logo or packaging?
Yes, OEM/ODM customization is available, including logo, key layout, and packaging.
CRC2303V
Can I customize the logo or packaging?
Yes, OEM/ODM customization is available, including logo, key layout, and packaging.
AN-MR25GA
Is this remote identical in function to the original LG AN-MR25GA?
Yes. It supports the same voice control, pointer, and wheel functions as the original model.
CRC2201V
Can it control LED fixtures with dimming or color adjustment functions?
Yes, it supports basic ON/OFF, dimming, and color adjustment functions. However, some special models released after May 2015 may not be fully compatible.
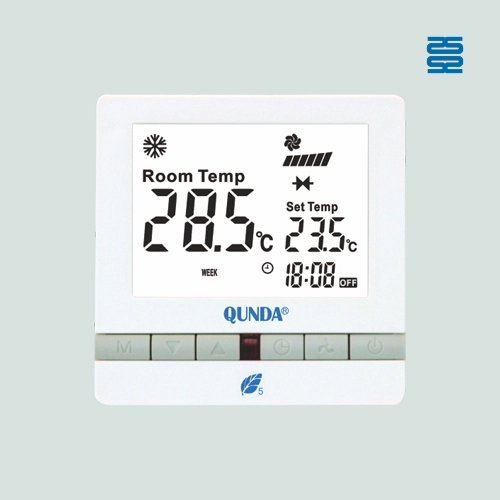
QD-U03C+
Can I adjust fan speed and temperature manually?
Yes. Fan speed (3 levels) and temperature (16°C–30°C) can be adjusted.
Recommended For You
The CRC2621V AI Universal Air Conditioner Remote is designed for the Southeast Asian market. With an AI search function and compatibility with 99% of air conditioner brands, it provides faster setup and a better user experience.
Infrared LED light remote for Panasonic Japan market. No setup required. Supports dimming, color adjustment, timer, and 3-channel switching.
Do solar remote controls still use lithium batteries? Learn how modern solar-powered remotes now adopt supercapacitors with USB Type-C fast charging for improved safety, durability, and long lifespan.
Learn how to check whether a garage door remote control bought online is compatible with your opener. Frequency, learning type, and easy tips explained.
Having trouble setting up a universal remote even though your TV brand is listed in the manual? Learn the real reason, common mistakes, and how to improve success by using precise TV codes.
You May Also Like

QD-HVAC23 Qunda Touch-Screen Thermostat for Air Conditioner

QD-HVAC06E Qunda Digital Thermostat for Central Air Conditioner
QD-HVAC05E Qunda Digital Thermostat for Central Air Conditioner

QD-HVAC03E Qunda Digital Thermostat for Central Air Conditioner
◼ Let’s Build Together
Get in Touch with SYSTO
If you have any comments or good suggestions, please leave us a message, later our professional staff will contact you as soon as possible.
Contact
Email us
Text or Call us
Address
Room 1606, No. 65, Zhongshan Seven Road, Liwan District, Guangzhou, Guangdong, China.








Facebook
Instagram
YouTube
Tik Tok
VK